Author
natalie@creospark.com
Why should we care about cybersecurity?
The importance of digital security in organizations cannot be emphasized enough in 2022. In order to stay proactive, today’s companies should take steps to protect their information from data breaches, unauthorized access, and other security threats to their business.
The average cost of a data breach has increased by $1.07 million over the pandemic, due to remote work. However, this shouldn’t be surprising, as there are more attack channels made available to hackers when employees are working remotely. With more informative and communicative networks being utilized by companies, hackers are naturally granted a larger target. With such potential for breaches, it is alarming that only 9% of businesses today recognize cybersecurity as a top priority, with a shocking 18% ranking cybersecurity as one of the least important company objectives.
Social engineering: how hackers easily obtain data
Social engineering is the term used for a range of malicious activities completed through human interactions. Users are tricked through emotional and psychological manipulation, which leads users into making security mistakes or giving away sensitive information.
First, an attacker will investigate a victim to collect information such as potential points of entry and weak security protocols. This is information that is needed to continue with the attack. Then, the attacker will attempt to gain the victim’s trust and encourage actions that break security practices, such as revealing confidential information.
Social engineering relies on human error and not on software or system weaknesses, making it highly dangerous. Mistakes that are made by real users are much less predictable, so they are harder to identify and stop than intrusions made by malware. Hackers prey on vulnerabilities and human emotion. A modern attempt at a socially engineered hack could look like an email from ‘your boss’ asking for sensitive information, or for you to perform actions that are not within your role.
Cyber security IS everyone’s responsibility. Some effective ways to implement security best practices include using strong passwords (minimum password length should be 13) and educating your employees. Cyber security requires regular staff training and monitoring, as hackers evolve just as quickly as security does. Through security awareness training customized to your business, employees are brought up to speed on a company’s IT procedures, policies, and best practices.
Solutions
Authentication methods
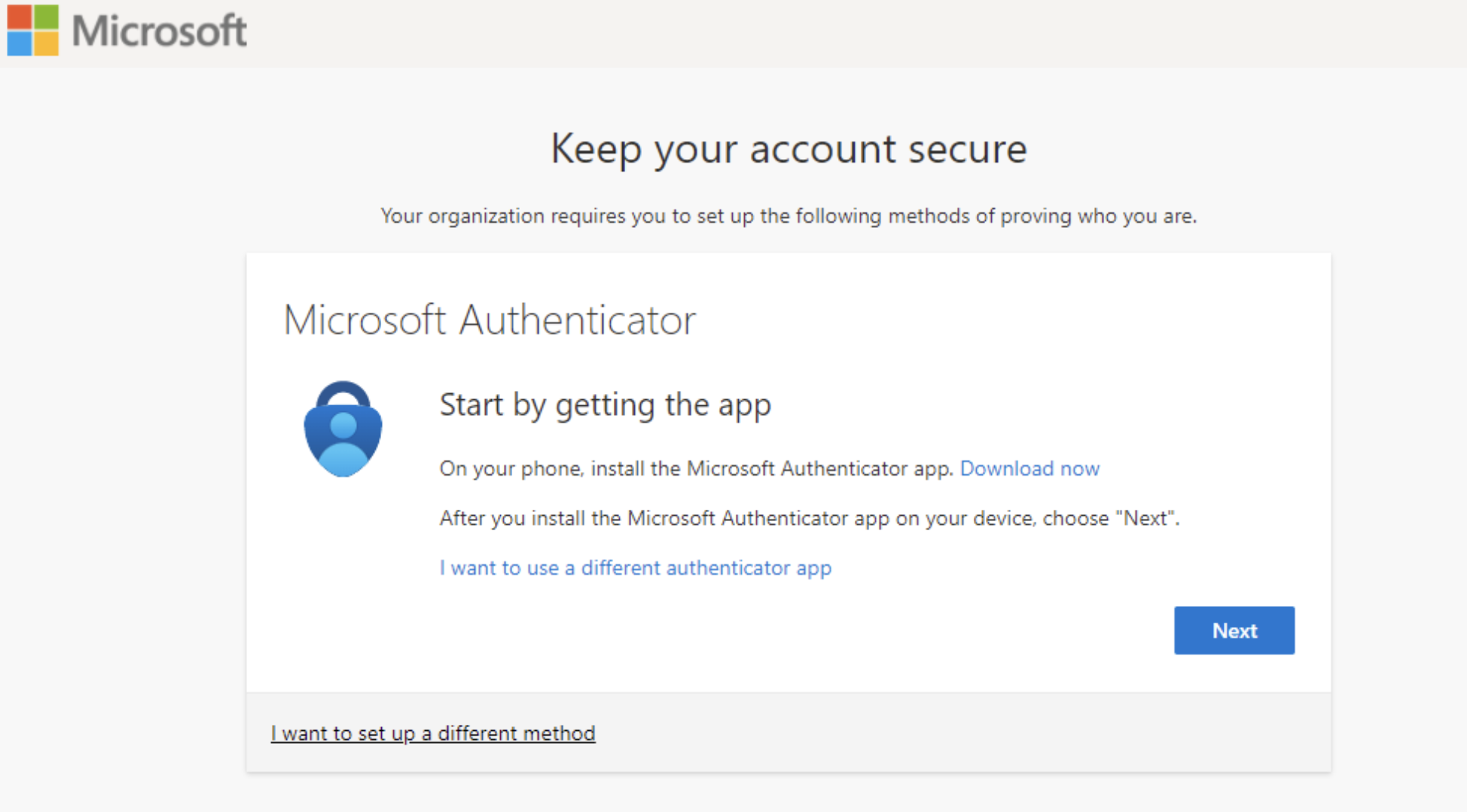
Users can typically sign in with a username and password, however, passwords should be paired with authentication methods that tend to be more secure. There are many other authentication methods, including security keys and Authenticator Apps. Azure AD Multifactor Authentication (MFA) adds additional security to sign in. In addition to a password, users can be prompted to respond to a push notification, enter a code, or respond to a text or phone call.
Check out this video by Microsoft to help you choose the best authentication method to keep your organization safe.
What is multifactor authentication?
Multifactor authentication is a process in which users are prompted during the sign-in process for an additional form of identification. This can be something like a code on their cell phone or a fingerprint scan. This authentication method decreases the likelihood of a successful cyber-attack.
How exactly does it work?
Azure AD Multi-Factor Authentication works by requiring two or more authentication methods. These can include something you know, like a password, something you have, like a token, smartcard, or phone, or something you are – a biometric, like a fingerprint or face scan.
You don’t need to change apps to use Azure AD Multifactor Authentication. The verification prompts are part of the Azure AD sign-in, which automatically requests and processes the MFA when needed.
Want to learn more about our Secure Cloud practice and how you can ensure your work gets done safely? Check out this blog!
Final thoughts
Multifactor authentication is a process that is relatively inexpensive and often easy to set up. It provides effective protection to individual users and the further business network. So don’t wait; enable Multifactor authentication now!
Have you checked in on your cybersecurity lately? Book a free consultation with us to ensure you’re keeping your people, business, data, devices, identities and applications safe.